I suppose it’s a playlist of cybersecurity for this week. This is yet another good usage of searching through known breaches covered yesterday’s post. If you are not using a password manager, like it or not, you are most likely guilty of reusing the same password. If you are not using a random password generator…
The Mad Tea Party
Inspiring yet Mad Spiels
Tagged Cybersecurity
App to Check Your Email Address in Security Breaches
Since I just covered a website tracking app related security breaches, I thought to add the old-fashioned one — the one tracks by your email address. Traditionally, service providers and security researchers had released their findings separately, per case basis. If you were a customer of 100 different services, you had to look out for…
How to Encrypt Disks on Windows
One of the trigger points behind my decision to build a dedicated PC has to do with general cybersecurity. To clarify, Boot Camp Windows running on Intel Mac is not particularly more vulnerable than the other Windows machine; it is simply more dated. And being dated, for the sake of security, means not gaining the…
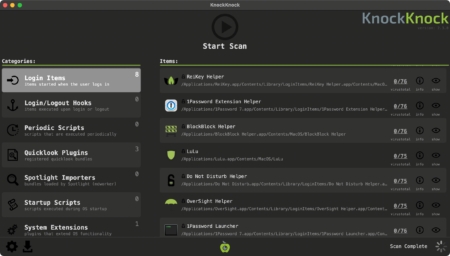
App to Manage macOS Login Items and System Extensions
I have been migrating from one Mac to another whenever I upgrade the machine. Often it is delivered with the convenience that I get almost identical experience as before, but only on the newer hardware. That said, the part of the ‘migration’ includes, though I didn’t verify it, copying over login items and system extensions…
How to Transfer to eSIM: Lessons From SKT SIM Breach
Though the title may sounds like a proper how-to, I ended up deciding to write it as “documentation” of what happened in my particular case. It obviously won’t work for everyone, and your mileage will vary greatly. I believe the common core issues for everyone would be that nearby carrier stores would not have enough…